Capturing credentials
by Ty Myrddin
Published on February 24, 2023
Some of the most common techniques adversaries use to capture credentials include finding or guessing credentials, and passing or relaying password hashes.
Finding credentials
Password storage targets on Windows after a compromise include operating system memory, user files such as Excel spreadsheets, and email inboxes and sent boxes, various system files like powershell history, the registry, and sticky notes.
Attackers might try harvesting credentials stored in webserver configuration files and application files, operating system memory, a web browsers' autocomplete history or password manager, hard-coded in applications, and in cloud applications.
The two most common ways for an adversary to intercept passwords is via an on-path attack, also known as Man in the Middle (MitM) attack, and via exploiting promiscuous protocols, such as LLMNR and NetBIOS, IPv6, and MDNS.
An example of the first is poisoning Address Resolution Protocol (ARP) tables in a network switching device, getting it to forward traffic to an unauthorised port before being forwarded to its intended destination, waiting for a password hash, then pulling the hash offline for cracking it. Promiscuous protocols that can be tricked into sending a password hash to an unvetted recipient can result in a breach if the password is not long enough and is not difficult to guess.
Guessing credentials
Insecure web applications in general can be abused to bypass application access control lists (ACLs) or forge valid tokens.
Adversaries confronted with a secure web application which does not leak platform, patch or configuration information; with code that protects against injection and scripting attacks; and with strong account access and lockout controls, may still try password guessing. Password lockout policies can sometimes be bypassed with password spraying.
Passing or relaying password hashes
- The Windows NTLM algorithm algorithm is susceptible to the well-known pass-the-hash attack.
- Newer Windows authentication algorithms such as Net-NTLM hashes make use of a one-time challenge. But if message signing is not both enabled and required by every host in the domain, these challenges can be relayed by attackers. Relaying attacks can be done via cross-protocol relays that use any other protocol that supports Windows Net-NTLM authentication.
- Even Kerberos authentication, though more secure, can be successfully attacked. In some cases, Kerberos can be abused to impersonate other users within the environment and forge a valid ticket.
And social engineering is still one of the most effective ways adversaries can use. Phishingseems to be the most popular choice. These attacks use persuasion techniques such as impersonating technical support personnel, name-dropping a person of authority, communicating a sense of urgency, and using plenty of technical jargon and alphabet soup to confuse users and elicit compliance. "For verification purposes, please give us the code we just sent to you."
Bypassing MFA
- The easiest way to bypass MFA is to social engineer.
- Another way could be to look for configurations that allow authentication that bypasses MFA, like application programming interfaces (APIs) or clients who do not require MFA, such as Exchange Web Services and Exchange Modern Authentication, which can provide a non-2FA-protected backdoor login.
- MFA-protected user accounts may not yet have been set up. For the adversary, time to do so. This is not quiet though, as the original user gets locked out of their account and will sound the alarm.
- A common bypass technique is to use the hashed Windows NTLM password hash to access functionality not protected by MFA.
- And last but not least, MFA systems need a fallback plan, and any weaknesses in a fail-open plan can be exploited.
Adding biometrics?
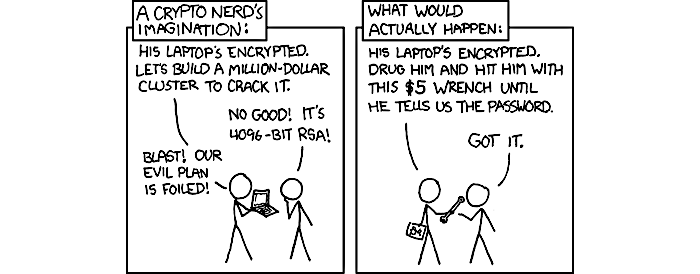
Adding fingerprint on top? FaceID? What if you are sleeping and someone uses your biometrics to unlock the device? What if someone knocks you out?
Impact
People, and companies and nations of all sizes have to defend against multiple threat events like ransomware, attacks going after personally identifiable information (PII) and the associated identity theft and possible further compromise, and scenarios in nation-state-sponsored global cyberwarfare, including boots-on-the-ground warfare contexts that involve digital communications. High time to really think things through.
Raw magic crackled from their spines, earthing itself harmlessly in the copper rails nailed to every shelf for that very purpose. Faint traceries of blue fire crawled across the bookcases and there was a sound, a papery whispering, such as might come from a colony of roosting starlings. In the silence of the night the books talked to one another. A student